Technical resources
Using OpenShift Pipelines CI/CD and Quay for Container Certification
OpenShift Pipelines is a Kubernetes-native CI/CD solution based on Tekton, providing a CI/CD experience through tight integration with OpenShift and Red Hat developer tools. OpenShift Pipelines is designed to run each step of the CI/CD pipeline in its own container, allowing each step to scale independently to meet the demands of the pipeline.
Red Hat Quay is a private container registry that stores, builds, and deploys container images. Quay analyzes images for security vulnerabilities, delivers geo replication and BitTorrent distribution to increase performance across distributed development sites and increase resiliency and redundancy for disaster recovery.
You may leverage OpenShift Pipelines and Red Hat Quay in tandem to rebuild and certify your container images automatically when new UBI base image updates are released. This automation will support and enhance your CI/CD container development workflows and will prevent security vulnerability concerns and outdated Red Hat certifications.
Prerequisites:
- Register as a partner here [in order to complete certification] if not already a partner.
- OpenShift Cluster [installed and hosted wherever you prefer]
- UBI container base image
- RHEL OS
- Review the container certification workflow documentation
- Create your container certification project within the Partner Connect portal
Install Red Hat Quay
You must use a private Quay image registry to store the desired base image that OpenShift Pipelines will consume and use as a source to trigger image builds. A Quay mirror registry is required and is only available using a private Quay instance.
*Note: Quay.io cannot be used.
Your private Quay registry is installed on an OpenShift cluster. Please ensure the OpenShift cluster has enough storage to host all available tags of the base image you rebuild.
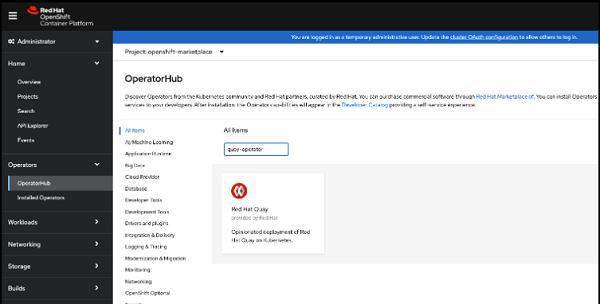
- As a cluster administrator, install Red Hat Quay Operator from the embedded OperatorHub
Configure Red Hat Quay
- Create a Quay private image repository for the application code
- Create a 2nd Quay private image repository for mirroring the desired UBI base image
- Configure this repository to point to your desired UBI base image in Red Hat’s official UBI repository
Create a Quay robot account which can read from the UBI repository and write to the application repository
- Download the credentials for this account to be used by OpenShift Pipelines later
Install OpenShift Pipelines
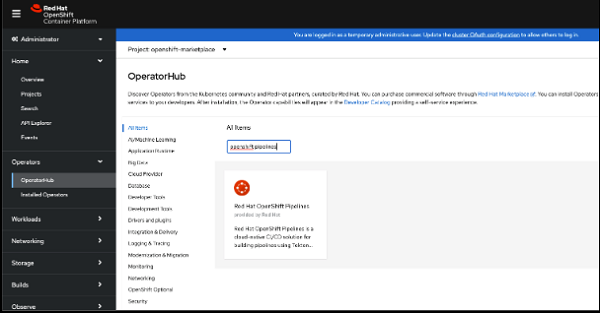
- As a cluster administrator, install the Red Hat OpenShift Pipelines Operator from the embedded OperatorHub within OpenShift
Create Your Pipeline
Create a pipeline that consumes a base image (i.e. UBI) along with application code and rebuilds every time that base image is updated.
Prerequisites:
- Create an OpenShift project for this pipeline
- Create a pipeline within this new project
- Create a tekton task for to run the preflight certification tool
- Task submits results and docker config file if and when all certification checks pass
- See all image requirements and their related checks
- View the preflight certification workflow
- You will need your certification project ID and your pyxis API key [both obtained from within your Partner Connect account]
- See preflight recipes
- An example of a preflight tekton task within our operator certification pipeline
- Task submits results and docker config file if and when all certification checks pass
- Create a tekton task for to run the preflight certification tool
- Create a secret from the Quay robot credentials created earlier
- Add the secret to the Service Account for the pipeline
oc secrets link default <pull_secret_name> --for=pull
[The default service account is default]
- Create a pipeline trigger, via a webhook. This trigger will initiate the pipeline to run.
- Learn more about OpenShift Pipelines webhooks.
Create a Quay Notification to Start the Pipeline
- Configure Quay to push a notification via a webhook to the OpenShift Pipelines webhook URL anytime a new UBI image is pushed to the repository
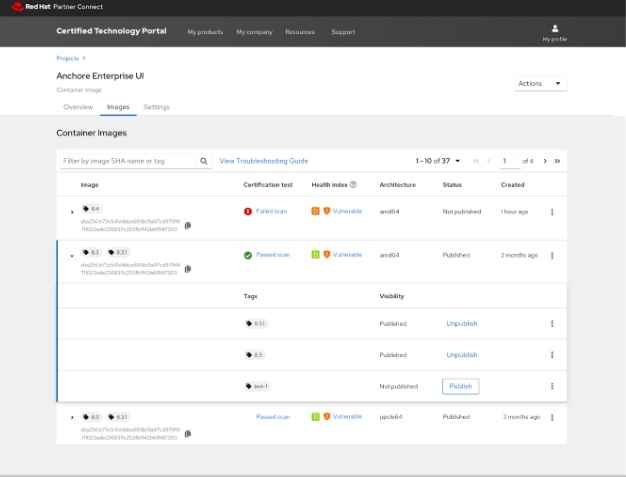
Publish Image
Once your image is built, certified, and results are submitted to the Partner Connect portal, you can then manually publish your image to be listed in the Red Hat Ecosystem Catalog. This step cannot currently be automated.
- From the Partner Connect portal, publish the newly certified image once it successfully passes vulnerability scanning.
Getting Help
Any issues related specifically to the certification steps can be directed to our Partner Success Desk.
If you have any questions related to this guidance and the functionality of the automated build pipeline, please reach out to epm@redhat.com to connect with our Engineering Partner Management team.
